What is process mining?
Process mining is a concept of data science to discover, analyze, enhance any process. It can deal with any journey left in your log data. Understand, visualize, and optimize your processes with logs from a variety of systems (ERP, CRM, MES etc.).
By analyzing the event logs through process mining, users can diagnose the process transparently. Through such, it is not only possible to check conformance of the real process, but also able improve efficiency via re-work elimination, lead-time optimization, and performance monitoring of resources.
Tackle any process-related questions with process mining.
Process mining can basically be applied to all (B2B, B2C, Public, Outsourcing …)
processes regardless of the field.
Customer Service
What is the biggest bottleneck of our customer service process?
Insurance
How much longer will the process lead-time be when we re-assess insurance?
HR
Which teams have process loops in their work process?
Is there a way to automate them?
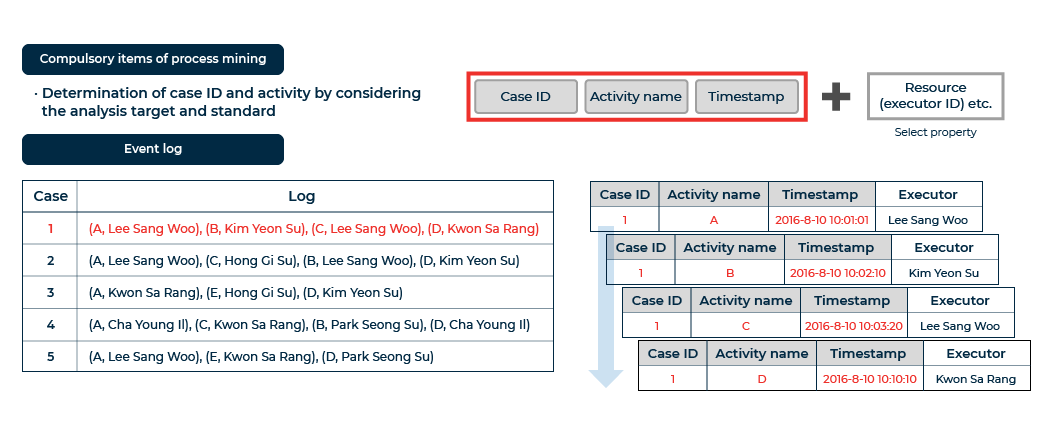
Event Logs
Simple set of data including information of Case, Timestamp, and Activity is required to start process mining.
A case consists of a sequence of multiple logs (events). With activity information, it is able to understand the meaning of each log(event). And also, you can also perform various analysis with additional resource information: such as executor.
Process Mining Use Cases
Process mining can be applied to a broad range of industries and domains.
Step beyond traditional metric-based analytics, and experience dramatic efficiency gains with Process Mining.
Public Sector
- Analyze workload & bottlenecks of business processes
- Identify work patterns via frequency analysis by worker and department
- Allocate tasks based on task relations, derived with social network analysis
Finance
- Enhance loan processing workflow
- Build standard insurance claim process & reduce lead time
- Establish a Business Intelligence (BI) dashboard for process monitoring
Manufacturing
- Visualize process & validate standard process (Conformance Check)
- Leadtime analysis by each stage of manufacturing
- Optimize scheduling under multiple projects
Healthcare
- Identify & improve bottlenecks in patient’s journey
- Mitigate delays by investigating incomplete patterns across tests/departments
Maritime/Logistics
- Analyze inefficiencies in container routes
- Optimize cargo loading processes by yard
Digital Marketing
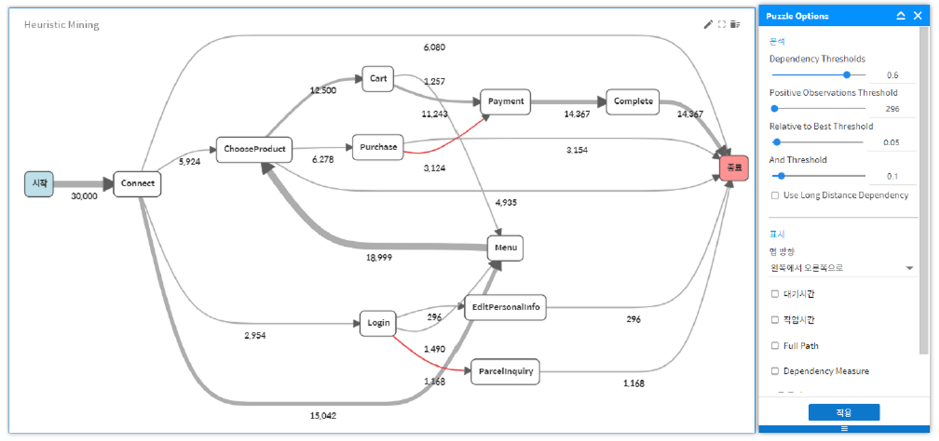
- Customer journey analysis to find bottlenecks and repetitions
- Extract process-wise insights from those who made the purchase through web/app
- Optimize web/app based on TRUE customer journey for more MOU
Process Mining Approaches
Process Discovery (Visualization and Analysis)
The most representative and basic process mining approach. It derives models through various algorithms (e.g. alpha, heuristics…) without any external information, and provides a simpler view of the problem. It is called “discovery” because it derives a process model without any existing process model.
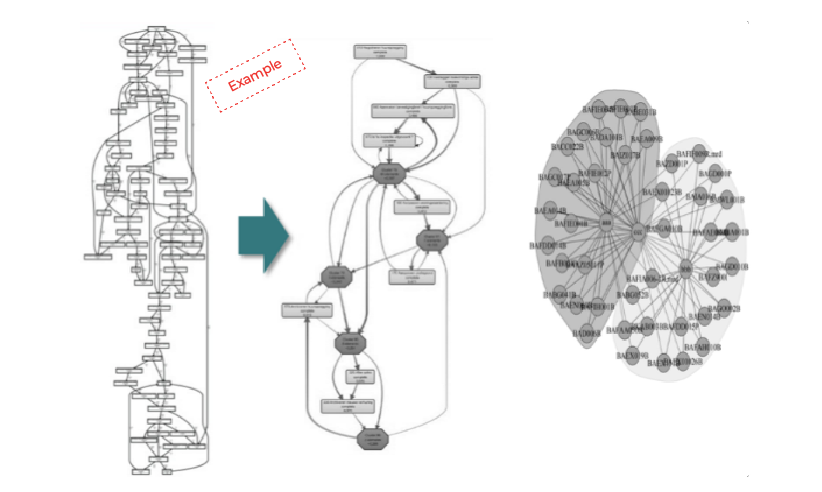
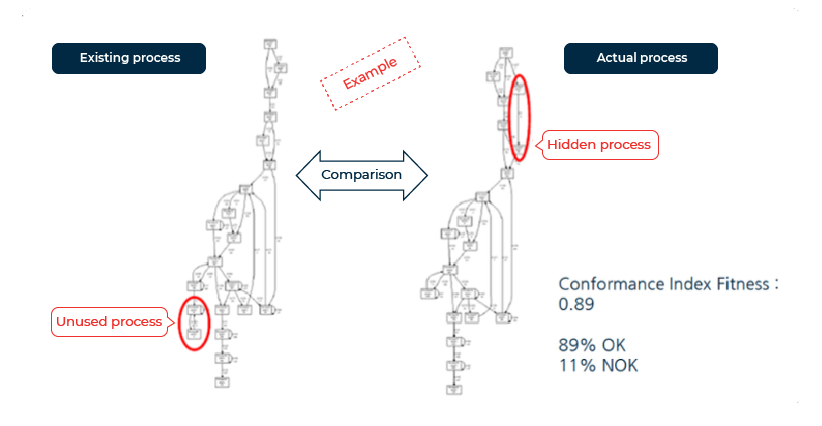
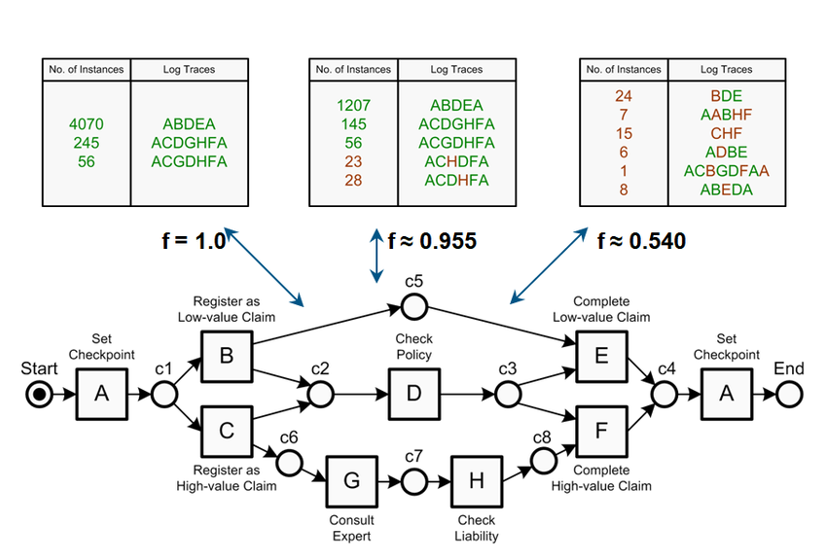
Conformance Check
(Process Monitor and Comparison)
Assess whether your standard process model is actually being fulfilled. Detect/quantify violations against the standard model and gain insights from real-life processes.
Process Enhancement
(Process Improvement)
Start your process mining journey with us
Experience unbelievable improvements in every aspect of your process,
through visualization with process models, discovery of key value areas in your process, lead-time analysis,
simulations and root cause analysis. Start with simple log data and PuzzleData’s ProDiscovery.
Explore the ‘True’ side of your data, that you would never see with simple KPI-based analytics.
Have an inquiry?
Get in touch with us.